Up One Level
You found the top source for complete information and resources for Installer Mspy Sur Android on the web.
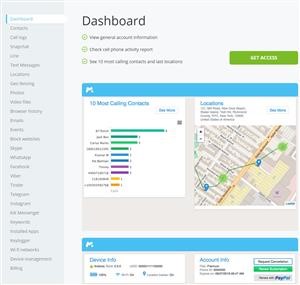
As soon as this is arrangement the software program will certainly operate with these settings up until you transform something. Here’s actually what you need to know about Google updates. Wi-Fi networks: You will be able to check all hotspots your kid’s device is connected with. When you buy it on your computer, on iPhone’s screen you’ll see its icon. If you're thinking about using mSpy, or if you are currently using it, and have some questions about it, then please read on for an FAQ about mSpy. In most cases, you will be able to monitor an Android phone, regardless of the brand, without having to root the device.
Once the monitoring has been set up it will continue to be active from then on. Seriously, my son’s safety costs way more than $30.” “I couldn’t believe my eyes what kids post on social media, such mean, hateful messages it broke my heart. This feature might be extremely helpful for foster families.
Here are Some Even more Details on Installer Mspy Sur Android
Right here are Some More Resources on Mspy Ios Review
Before you start, you need to ensure that the iCloud Backup is activated, otherwise, you need to turn it on: Go to the target device Settings; Click on iCloud; Choose iCloud Backup and turn in on; Press the button Back Up Now. The reliable parental control app like mSpy is a perfect tool for this purpose. What's really interesting is that I NEVER received an alert from Apple saying that someone had logged into my iCloud account from another device. All the further backups will be done automatically if the following conditions are met: Your target device is charging; Your target device is connected to the Wi-Fi Network; Your target device is not in use (the screen is locked). Will mSpy work on Windows phone? – No, unfortunately, mSpy is not compatible with Windows phones. One can use the app to get an exact location of their friends and family.
Right here are Some More Resources on Mspy Ios Review
Advanced Features The above mentioned options are likely to be available without rooting, but if you are looking for advanced monitoring features, you may need to root the device. If the person is present anywhere in the world, he can be caught or tracked easily. When typing the code, you confirm you trust the device. However, it does have its fair share of pros and cons as well.
Here are Some More Resources on Installer Mspy Sur Android
Initially designed for quick chats among friends and relatives, it often results in cyberbullying attacks, communication with online predators, and personal data theft. They provide the preview of your text messages on their main screen. When you've completed the installation the software program will certainly begin keeping track of the phone instantly. If somebody else puts wrong credentials, provide wrong security answers more than 3 times, Apple automatically locks the account to protect your safety. If your device has Marshmallow (Android 6+), the latest features are still available to you.
Previous Next
See Also
Mspy Pro Apk Free Download
cp.mspyonline Login
Mspy Auf Dem Iphone Finden
Terms of Service
Disclosure Statement
DMCA
Privacy Statement
Contact